

This image is licenced by IStockPhotos
“The most that can be expected from any model is that it can supply a useful approximation to reality: All models are wrong; some models are useful.”
- George E. P. Box
Maturity models represent a systematic approach to organizational assessments and improvement that has evolved from early management science theories into sophisticated frameworks. We’ll examine the historical development of maturity models like the Capability Maturity Model (CMM/CMMI), with a specific focus on the OWASP Software Assurance Maturity Model (SAMM), the Building Security In Maturity Model (BSIMM), the Cloud Native Computing Foundation (CNCF) Cloud Native Maturity Model (CNMM), and the Cloud Security Maturity Model (CSMM). I’ll discuss some security frameworks, such as the NIST Cybersecurity Framework (CSF), even though it is not technically a maturity model, but someone will inevitably ask about it.
Capability Maturity Model Integration (CMM/CMMI)
Capability Maturity Model Integration is a structured framework for assessing and improving an organization’s software development processes. Initially developed as the Capability Maturity Model (CMM) in 1987 by the Software Engineering Institute (SEI) at Carnegie Mellon University (CMU) to evaluate government contractors’ software development capabilities, the successor, CMMI, has evolved into a foundational methodology for continuous process improvement. CMMI is grounded in the principle that the quality of a system or product is significantly influenced by the method used for its development and maintenance. The model emphasizes three fundamental principles: clear process definition, consistent process improvement, and alignment of processes with organizational goals.
CMMI organizes process improvement into five progressively sophisticated maturity levels, each representing a distinct stage in organizational improvement: Initial, Repeatable, Defined, Managed, and Optimizing.
Reference: https://cmmiinstitute.com/cmmi/intro
OWASP Software Assurance Maturity Model (SAMM)
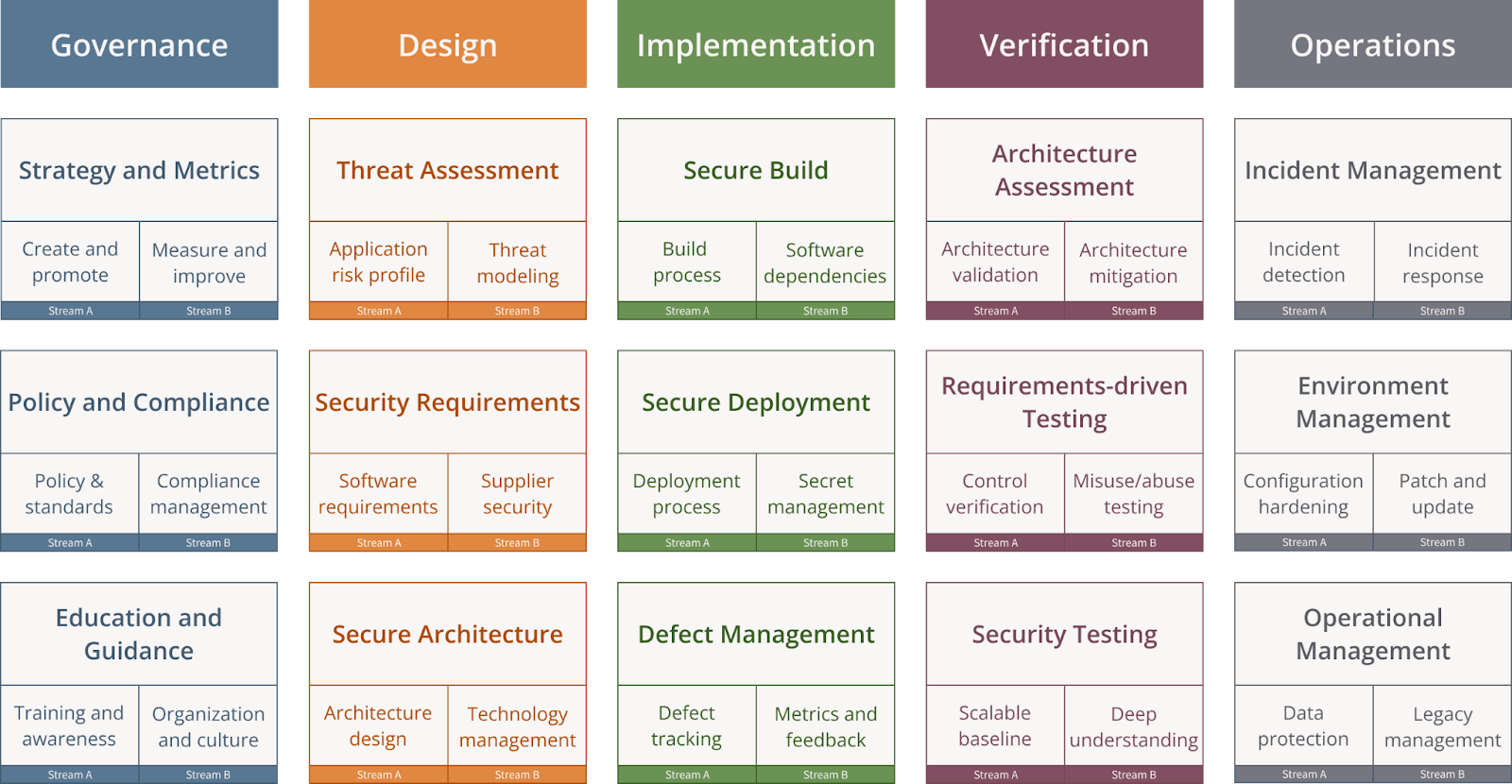
The OWASP Software Assurance Maturity Model (SAMM) is a prescriptive, open model that provides organizations with an effective, measurable way to analyze and improve their software security posture throughout the software development life cycle (and beyond). SAMM’s origins date back to 2009, when the original model, OpenSAMM 1.0, was authored by Pravir Chandra and sponsored by Fortify Software. SAMM is one of the OWASP flagship projects, serving as a roadmap for building secure, resilient software by helping organizations assess their current state, define targets, and implement security improvements in well-defined iterations. I’ve worked with SAMM for almost 15 years now and have been part of the core team for close to a decade. I believe it’s one of the best models for building and maintaining a secure development lifecycle.
SAMM is built on four foundational principles that guide its design and application:
- An organization’s behavior changes slowly over time. Changes must be iterative as you work towards long-term goals. They must be integrated into the policy, process, technology, and most importantly, the culture of an organization.
- There is no single recipe that works for all organizations. We must enable risk-based choices tailored to the organization. Recognizing that security needs can differ significantly between a financial institution with stringent compliance requirements and a technology startup with rapid development cycles.
- Guidance related to security activities must be prescriptive. A solution must provide enough detail for non-security roles. Actionable guidance provides detailed recommendations to improving security practices.
- Overall, the model must be simple, well-defined, and measurable. It’s often said that you can’t improve what you can’t measure. Metrics will drive behavior. You have to be careful that your metrics drive the desired behavior. SAMM tried to ensure that it’s driving the right behavior, and teams are rewarded for doing so.
SAMM is organized around five business functions, each containing three security practices, each with two logical streams and three maturity levels.
The scoring in SAMM is granular enough to show incremental improvement when changing a single answer to one of the 90 questions. Rather than forcing someone to answer yes/no to questions, SAMM uses a graduated response system: no (0), few/some (.25), at least half (.5), and many/most (1).
SAMM defines three maturity levels:
- Level 1 is foundational
- Level 2 is mature
- Level 3 is advanced
The granular scoring allows teams to get credit for work they are doing to improve security and reduce risk without enforcing a rigid pattern they have to follow, regardless of whether it would benefit their specific organization.
Reference: https://owaspsamm.org/
Building Security In Maturity Model (BSIMM)
The Building Security In Maturity Model (BSIMM) is a descriptive, data-driven framework designed to help organizations assess, benchmark, and improve their software security initiatives by comparing their practices against real-world observations from other organizations. BSIMM originated from OpenSAMM, but evolved into a distinct approach focused on observation rather than expert prescription. BSIMM has maintained an annual update cycle since its inception. BSIMM is organized into four domains, each containing three security practices.
- Governance: Strategy & Metrics, Compliance & Policy, Training
- Intelligence: Attack Models, Security Features & Design, Standards & Requirements
- SSDL Touchpoints: Architecture Analysis, Code Review, Security Testing
- Deployment: Penetration Testing, Software Environment, Configuration Management & Vulnerability Management
This essentially mirrored SAMM for many years, with each having very similar functions/domains and security practices. They have diverged over the last several years, especially when SAMM released v2.0 with a fifth business function. BSIMM defines maturity across four levels:
- Level 1 is Emerging
- Level 2 is Defined
- Level 3 is Measured
- Level 4 is Optimized
Some of the advantages of BSIMM include data-driven insights, benchmarking, an understanding of what other large organizations are doing, and maturity progression. Some disadvantages of BSIMM include the cost of completing an assessment, its proprietary nature, the inability to prescribe recommendations, and a focus on large enterprises.
Reference: https://www.blackduck.com/services/security-program/bsimm-maturity-model.html
CNCF Cloud Native Maturity Model (CNMM)
The Cloud Native Maturity Model (CNMM) is a framework developed by the Cloud Native Computing Foundation (CNCF) that assesses organizational maturity in cloud native adoption and provides guidance for improvement from initial adoption to full maturity. First launched in 2021 and updated through version 4.0 in 2025, it serves practitioners, team leaders, and executives by bridging technical goals with business outcomes.
The CNMM organizes cloud native transformation around four (or five) key dimensions:
- People: Skills, organizational structure, team composition, and security culture development
- Process: Workflows, CI/CD implementation, infrastructure as code (IaC), and shift-left security practices
- Policy: Internal and external policies for security, compliance, and governance requirements
- Technology: Technical infrastructure including GitOps, observability, security, storage, and networking
Some parts of the documentation list a fifth dimension:
- Business Outcomes: Alignment between cloud native initiatives and business goals, including risk management, compliance, customer satisfaction, and cost efficiency.
The CNMM has five defined maturity levels:
- Level 1 – Build: Baseline cloud native implementation in place and in pre-production
- Level 2 – Operate: Cloud native foundation established and moving to production
- Level 3 – Scale: Growing competency with defined processes for scaling operations
- Level 4 – Improve: Enhanced security, policy, and governance across the environment
- Level 5 – Adapt: Optimization through revisiting earlier decisions and continuous monitoring
An important principle in CNMM is that each level represents a floor, not a ceiling; organizations must achieve all provisions across all dimensions at a given level before claiming that maturity level. Although, to be honest, I couldn’t find a list of “all provisions”
for each dimension, only a bit of a narrative.
I was unable to find any graphics or summaries of the model, nor any scoring. In one area, they list the four key “dimensions,” but then list five “aspects” of cloud-native maturity: the four dimensions plus “business outcomes.” Digging deeper, I found a reference to “five key dimensions”; I guess it’s still a work in progress, as version 4 is labeled in beta.
Reference: https://maturitymodel.cncf.io/
IANS Research/Securosis Cloud Security Maturity Model (CSMM)
The Cloud Security Maturity Model (CSMM) is a framework developed by IANS Research and Securosis in partnership with the Cloud Security Alliance (CSA) that helps organizations assess and improve their cloud security posture through a structured, cloud-specific approach. The first version was released in early 2020, with the update to version 2 in 2024. The model focuses on unique cloud security challenges rather than general security practices, offering a systematic approach to evaluating risk and advancing cloud security capabilities.
CSMM is organized around three key domains covering 12 categories:
- Foundational Domain: Governance, Organization Management, IAM, Security Monitoring
- Structural Domain: Network Security, Workload Security, Application Security, Data Security
- Procedural Domain: Risk Assessment and Provider Management, Resilience, Compliance and Audit, Incident Response
CSMM also has five maturity levels that are very similar to the CMMI levels:
- Level 1: Initial
- Level 2: Repeatable
- Level 3: Defined
- Level 4: Capable
- Level 5: Efficient
There is an online assessment option to help you understand your current state (which requires registration so they can collect your info), a couple of information documents you can download, and an Excel spreadsheet of the detailed model.
Reference: https://www.iansresearch.com/resources/cloud-security-maturity-model
NIST Cybersecurity Framework (CSF)
The NIST Cybersecurity Framework (CSF) is a voluntary, risk-based framework developed by the National Institute of Standards and Technology (NIST) to help organizations manage cybersecurity risks. Originally released in 2014 and updated to v2.0 in early 2024, the framework provides a comprehensive cybersecurity approach adaptable across industries and organizations. The NIST CSF is organized around three primary components: Framework Core, Framework Profiles, and Implementation Tiers.
The Framework Core is at the heart of the CSF and consists of a hierarchical structure of Functions, Categories, and Subcategories. In version 2.0, the framework includes six core functions: Govern, Identify, Protect, Detect, Respond, and Recover. These six functions are further organized into 22 categories and 106 subcategories that provide increasingly specific cybersecurity outcomes. The functions are designed to be performed concurrently and continuously rather than as sequential procedural steps.
The Framework Profiles enable organizations to create a blueprint for managing cyber risks aligned with organizational goals. Organizations should develop a “Current Profile” documenting existing practices and a “Target Profile” defining desired outcomes.
One challenge of using the CSF as a maturity model is that there isn’t a measurable system within the framework.
Reference: https://www.nist.gov/cyberframework
About The Author
Brian is a Principal Security Consultant at Cloud Security Partners. He has over 21 years of experience in various roles in IT, with the majority in application development and security. In his "day job," he serves as department chair of computer science and cybersecurity at Union University in Jackson, Tenn. He helped build FedEx's Application Security team, worked on the Trustworthy Computing team at Microsoft, consulted on software security for years, and served as a project lead and active contributor for SAMM v1.1-2.0+ and OWASP Top 10 2017, 2021, and beyond.
Brian is a contributor to the RABET-V Program for assessing non-voting election technology. He holds several cybersecurity and IT certifications and is working on his Doctor of Computer Science degree in cybersecurity and information assurance.
Stay in the loop.
Subscribe for the latest in AI, Security, Cloud, and more—straight to your inbox.
